 Let the Smart Energy transition begin…
Read More
Feb 08, 2023
Let the Smart Energy transition begin…
Read More
Feb 08, 2023
 Introducing the fifth generation of smart meters: The NES story
Read More
Jun 08, 2022
Introducing the fifth generation of smart meters: The NES story
Read More
Jun 08, 2022
 “NES, a next generation AMI solution provider for India’s Smart Grid Market”
Read More
Mar 23, 2022
“NES, a next generation AMI solution provider for India’s Smart Grid Market”
Read More
Mar 23, 2022
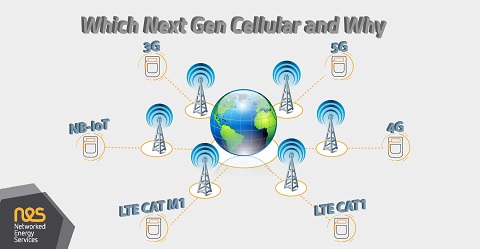 Which Next Gen Cellular and Why
Read More
Jan 21, 2022
Which Next Gen Cellular and Why
Read More
Jan 21, 2022
 Modern Protocol for the Smart Grid
Read More
Nov 12, 2021
Modern Protocol for the Smart Grid
Read More
Nov 12, 2021
 The Clean Energy Package and the Smart Metering Business Case
Read More
Nov 05, 2021
The Clean Energy Package and the Smart Metering Business Case
Read More
Nov 05, 2021
 AMI and Power Line Communications
Read More
Jul 01, 2021
AMI and Power Line Communications
Read More
Jul 01, 2021
 How to Address Cybersecurity Vulnerabilities in the Low-Voltage Grid
Read More
Nov 26, 2020
How to Address Cybersecurity Vulnerabilities in the Low-Voltage Grid
Read More
Nov 26, 2020